CMMC Expertise, at Every Step
Protecting the Defense Industrial Base is our mission.
From readiness to certification and beyond, we bring unmatched experience to deliver everything you need for Cybersecurity Maturity Model Certification.
Redspin, an Authorized C3PAO for...
CMMC Services for:
Prime Contractors
Sub Contractors
ESPs
MEPs
Academic Research
Universities

Our clients ask us…
…to solve their unique security and compliance challenges related to Cybersecurity Maturity Model Certification (CMMC) and to help them build and execute strong cybersecurity programs that will position them for success as a Defense Industrial Base (DIB) contractor.

How can I Achieve CMMC Certification?
We help you figure out what you need to do to be CMMC ready and certified.
How do i improve Cyber defenses?
We help you understand if you are doing enough to prepare and prevent a cyber incident.
How do i fix identified gaps?
We can help you validate your people, processes, and technology are working as expected.

Am i protecting sensitive data?
We help you ensure you have the right safeguards in place to protect our Nation’s sensitive data.

How We Keep You Secure and Compliant
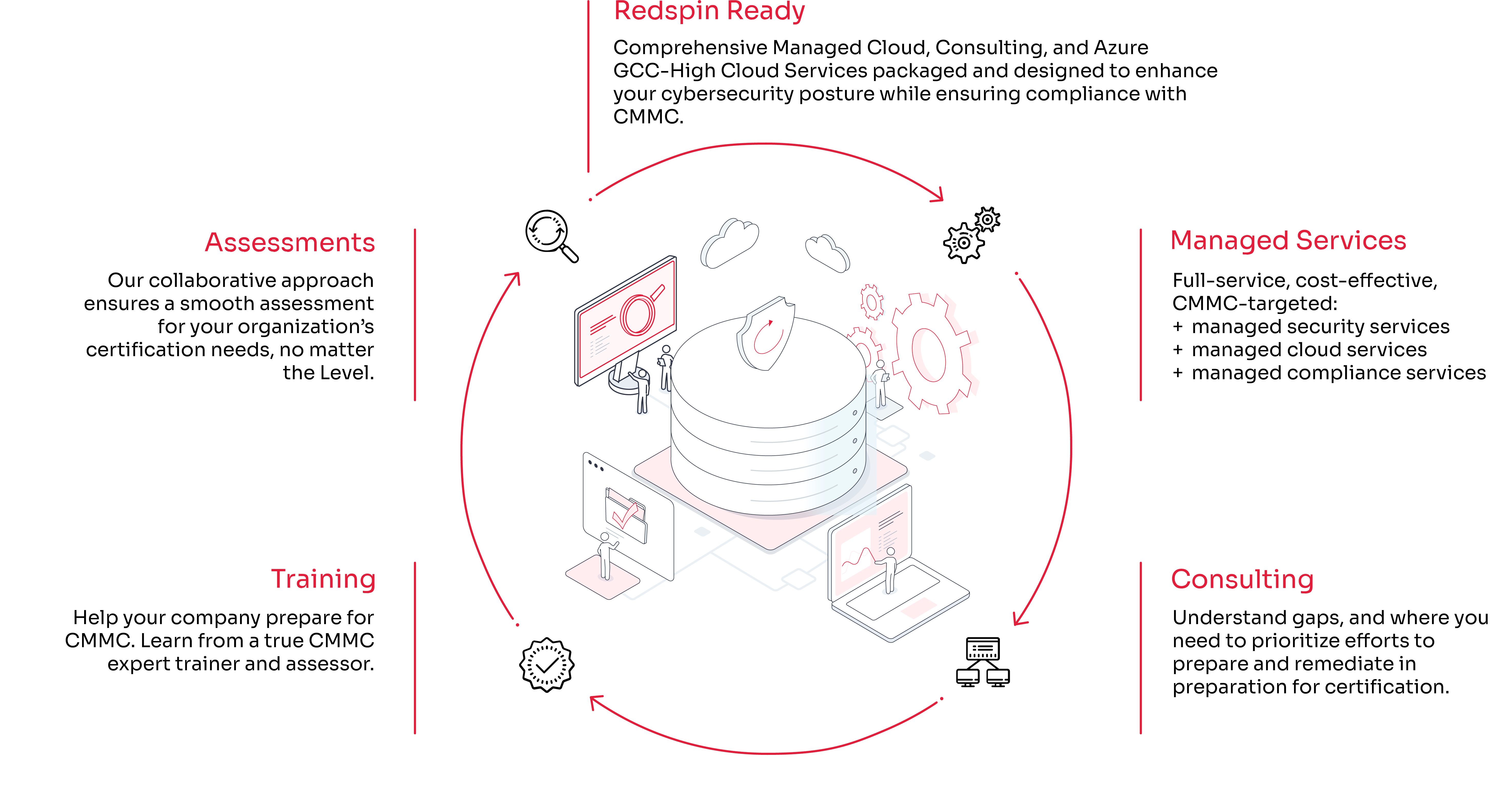
Our Redspin Ready Managed Cloud Program offers robust security, scalability, and efficiency, tailored to meet the unique needs of your organization:
+ Secure Cloud Architecture: Implementing best practices for cloud security to protect CUI/FCI
+ GCC-High Enclaves: Providing high-security cloud environments compliant with government standards.
+ Compliance Assurance: Ensuring your cloud environment meets CMMC requirements.

Diverse Industry Experience
As the first authorized C3PAO, Redspin leads the industry in CMMC services. Our team of experts provides end-to-end support, from assessment prep to certification and beyond, ensuring your organization is fully prepared to meet CMMC.
We understand every organization is on its own CMMC journey, and more importantly we understand there are business nuances, specific regulations, and practices unique to different industries.
With our Department of Defense (DoD) backgrounds and industry experience across disciplines supporting clients in highly regulated industries, we have the techniques and know-how to apply industry-specific or broad industry learnings to your environment.
Technology
As a leader in the CMMC space, we help organizations secure sensitive data and IT processes.
Are you CMMC compliant?
Defense Contractors
Defense Industrial Base (DIB) suppliers have a very important role in securing the nation’s supply chain.
Is your cyber hygiene at the level needed to meet CMMC certification in order to win DoD contracts?
Supply Chain
The DoD supply chain is one of the most targeted for cyber attacks.
Is your environment secure?
Do you know the sensitive data your business handles and keeps?
Do you have an approach that can respond, and meet CMMC requirements?

Our Approach is Tailored to Meet Your Needs, No Matter Where You Are On The Journey.
Redspin’s Managed Services offer a holistic approach to CMMC, integrating advanced technologies and expert support to protect your organization. Our services include:
- Managed Security Services: Comprehensive protection against cyber threats.
- Managed Cloud Services: Building, and ensuring secure and efficient cloud operations.
- Managed Compliance Services: Maintaining compliance with CMMC.
Ready to tailor your journey?
Award-Winning CMMC & Managed Cloud Services
Recognized for excellence in cyber defense, compliance, leadership & Innovation

National Cyber Defense Cybersecurity Industry Solution of the Year (Redspin Ready Managed Cloud Services)

CMMC Compliance Service of the Year

Critical Infrastructure Cybersecurity Solution of the Year (Redspin Ready Managed Cloud Services)

Leadership Excellence in Business

MSSP Alert’s Top 250 MSSPs for 2024 (Redspin, under a Division of Clearwater)
Securing The Nation's Defense Industrial Base
Get started with Redspin Today
Helping you navigate CMMC.